The teenager joins an unsecured airport Wi-Fi to keep watching a stream. Within an hour, an attacker on the same network has scraped persistent device identifiers - the same pattern the FBI's juice-jacking PSA describes for charging stations and free Wi-Fi.
Boundless 2.0
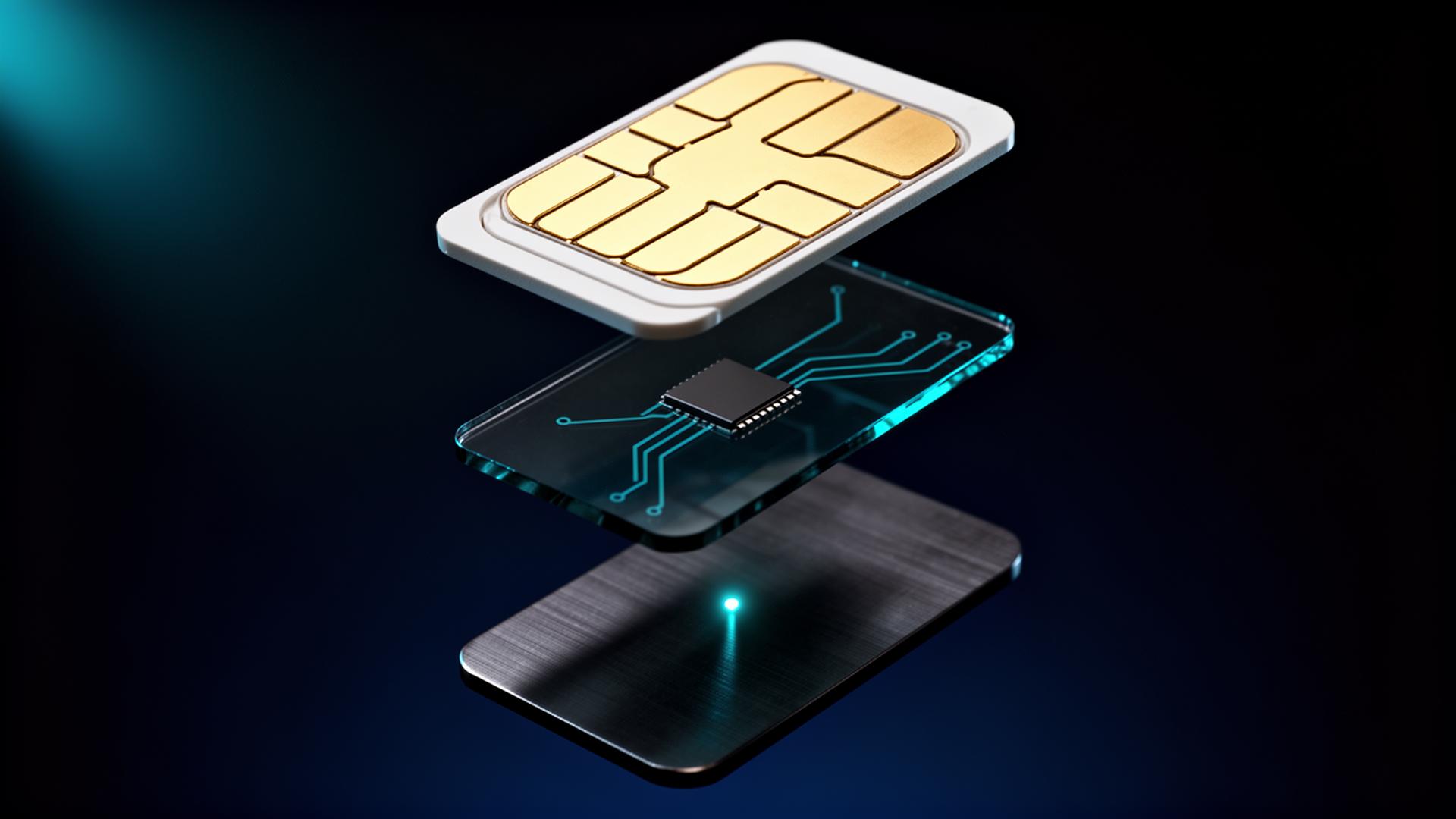
Every device on a 2.0 family root prefers the hardware-rooted cellular identity over an unverified Wi-Fi join, and the line itself rejects SIM-swap requests without cryptographic proof of re-issue from the principal's named owner.